5 preconceived ideas about encryption!
Encryption ABC's
Too many preconceived ideas about encryption stop companies from taking action. Such reticence can be costly when sensitive data is leaked and disclosed. A look at five stubborn misconceptions…
1. Encryption is too complicated to implement
Smart cards, thumb drives, public key infrastructure (PKI)… Until a few years ago, even the most motivated could be discouraged by the complexity of encryption procedures.
Today, solutions include native management of an encryption strategy inside the information system. They don’t need any extra hardware or servers, nor do they require changes to storage space organization.
To protect desktops, just deploy the encryption solution on all of them in the same way as other cybersecurity systems.
Deployment can be by mastering or by using an
MSI format file as part of a user group policy (GPO).
2. If I encrypt my data, I risk not being able to get it back
Another recurring fear is loss of data. A malicious act, a forgotten password or the simple departure of an employee can make the information inaccessible if nothing is planned for that type of risk.
Encrypted file recovery is therefore an essential item to be vigilant about. It’s part of the recovery strategy, namely all the resources that allow data to be accessed when major events occur. This strategy must be defined in advance. Security teams must have full recovery and troubleshooting capabilities if keys are lost, for staff changes, for compliance audits, or for requests from the judiciary.
These recovery keys are protected by a fully fledged physical or logical capability and are subject to a formalized process.
In what context, how, and by whom are recovery accesses used?
A recovery key can be placed in a safe, and only certain people will be able to use it.
Role separation can also be implemented. For example, for personal health data, it may be decided that only the Information System Director has access to the encrypted data, while the medical department has the recovery card PIN code, and Senior management the card itself, but not the code..
3. Workstation performance will collapse
Another concern is the impact of encryption on workstation performances (CPU, RAM). Will they slow down significantly?
In fact, data encryption/decryption operations are completely transparent. Using an optimized on-the-fly encryption solution, users don’t notice any changes in performances.
4. Encryption will have too high an impact on the IT teams and the users
Another misconception is that encryption would create an extra workload for the IT teams that monitor the work environments. Using their usual tools (GPO), they can very simply set up the encryption rules in accordance with the security policy defined by the company.
In fact, nothing changes for the IT department. The only difference? It doesn’t have access to decrypted data, only users who have the key can. As far as such users are concerned, the encryption solution must be as transparent as possible to avoid attempted workarounds.
In our white paper, entitled “Successfully Conducting Your Encryption Project: 6 keys for CIOs and ISMs” we insist on this notion of transparency, which is a guarantee of support. Even so, “it’s very important not to mistake transparency with the fact that users may not be actively involved in applying the security philosophy. This would risk them losing their sense of responsibility. On the contrary, they should be reminded that the information being handled is confidential and that everyone is responsible for security. “
5. I can’t encrypt my sensitive data because I don’t know where it is
Over the years, data accumulates in layers creating silos inside the information system. If you don’t know exactly where the critical data is, all the data can be encrypted, regardless of where it is.
Exit the classification of sensitive data phase, the company starts with a restricted perimeter and then extends the protection to all its information assets
In a systemic approach, an encryption policy must be generalized to the extended information system. It covers the company perimeter – workstations, servers, removable media, … – but also cloud resources and online storage spaces in particular.
So these preconceived ideas?
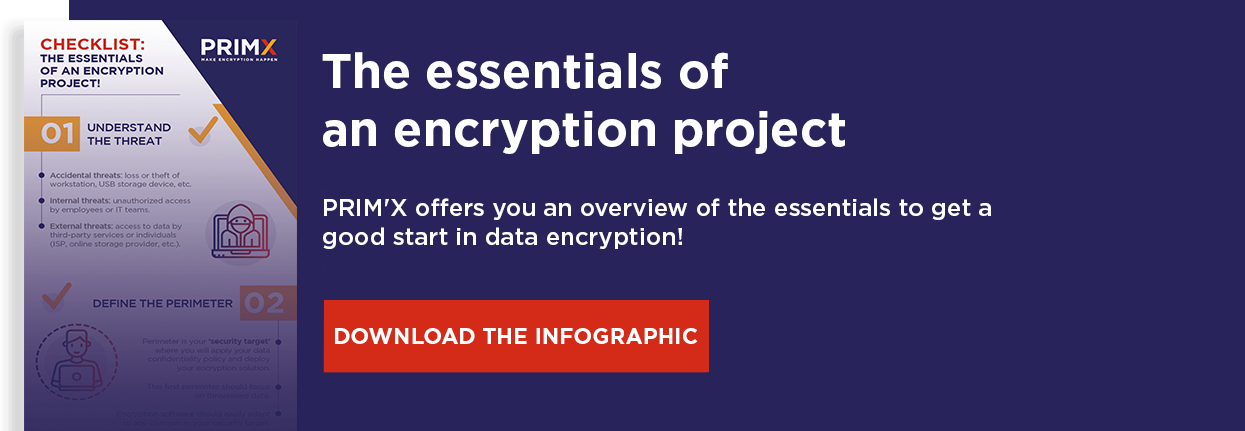
Getting rid of preconceived ideas about encryption isn’t so complicated after all. If you still have doubts or questions, we take a look at the essentials of an encryption project in this infographic.